[The 2026 Perspective]
A Note from the Architect
When the system runs hot—during a transition to Dubai or a redomiciliation of global entities—the brain takes shortcuts. These shortcuts are legacy code from a ‘Renter’ mindset. In 2026, I treat these 12 traps as systemic bugs. If you don’t name the leak, you can’t seal it. My primary bug remains All-or-Nothing thinking; I’ve had to learn that an Architect builds in increments, even when the vision is monolithic.
The Hardened Log
You are rarely battling the market; you are battling the internal entropy of your own logic. Under high-pressure loads, the human OS defaults to primitive shortcuts that create permanent structural damage from transient noise.
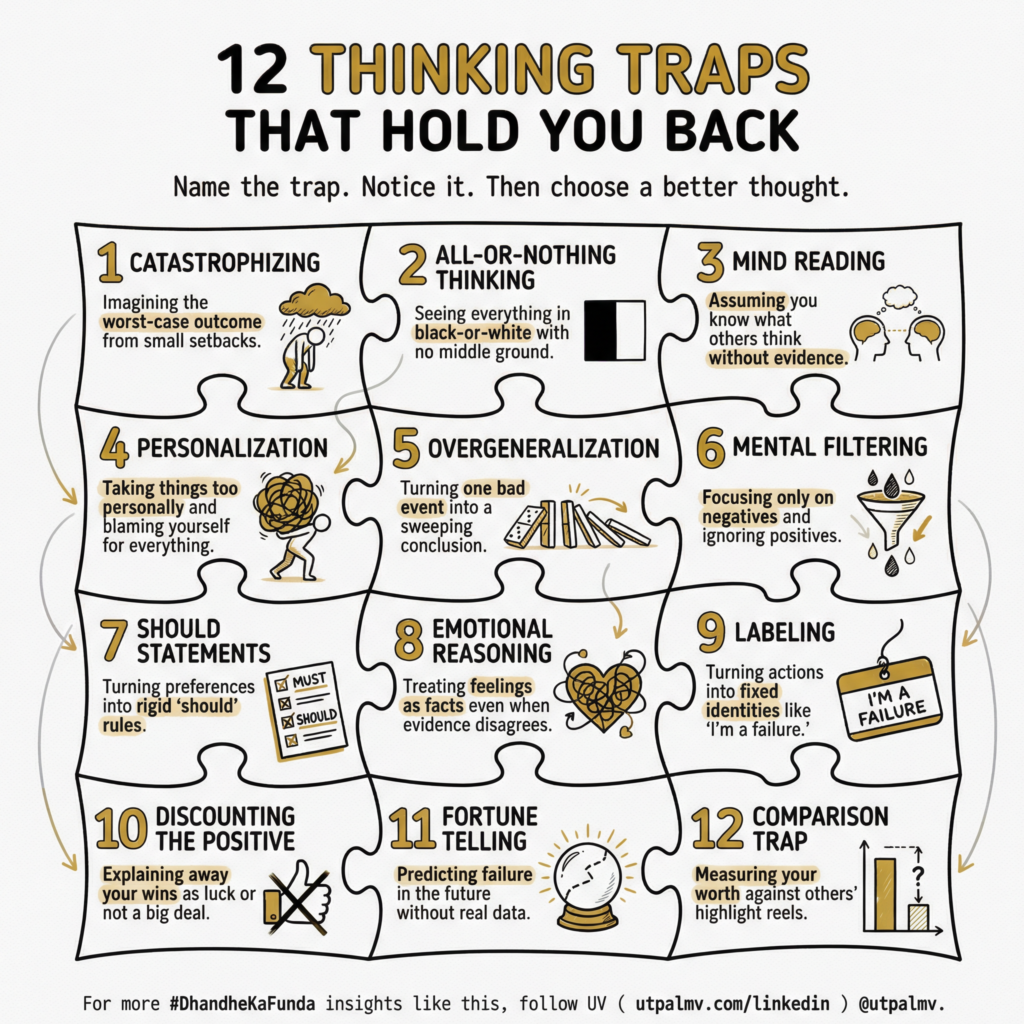
The 12 Logic Leaks to Audit
-
Catastrophizing: Translating a minor setback into a total system failure.
-
All-or-Nothing Thinking: The refusal to acknowledge gradients. If the structure isn’t perfect, you deem it worthless.
-
Mind Reading: Operating on unverified assumptions regarding other nodes in your network.
-
Personalization: Attaching your identity to global market movements or systemic errors.
-
Overgeneralization: Mapping a single data point as a permanent law of the system.
-
Mental Filtering: Focusing on a single leak while ignoring the integrity of the entire structure.
-
Should Statements: Rigid, legacy rules that create friction in a dynamic ecosystem.
-
Emotional Reasoning: Mistaking high-intensity “Lizard Brain” signals for clinical data.
-
Labeling: Converting a transient mistake into a permanent identity tag.
-
Discounting the Positive: Refusing to log successful data points as “luck” while over-indexing on failures.
-
Fortune Telling: Predicting systemic collapse without supporting data.
-
Comparison Trap: Calibrating your internal architecture against someone else’s polished facade.
The Sovereign Protocol: Name the leak. Notice its occurrence in real-time. Apply the logic override to maintain systemic momentum.